Before talking about how we secure our devices, we need to be clear about what we are securing them against. This is where the idea of a threat model comes in. A threat model is simply a description of the risks we consider and the assumptions we make about the environment our devices operate in. It guides how we design hardware, software, and operational practices.
Once you place hardware inside a care room, the security conversation becomes very concrete. People naturally ask what the device is doing. How does it work? Can it see me? Can it hear me? Can it track me? These are not devices tucked away in a locked server rack. They sit in someone’s living space, sometimes during the most difficult moments of their life, and we have a responsibility to address these concerns and ensure the device feels safe to be around. Our devices operate in semi-monitored spaces where individuals, visitors, and staff move around them every day. That environment shapes how we think about threats and what we need to protect against.
We assume that someone may get brief, opportunistic access to a device. Maybe a visitor is curious, maybe someone else interacts with it. That kind of momentary access should not be enough to open a device, plug something in, or trigger a mode that bypasses normal protections. At the same time, we cannot completely rule out more capable attackers, people with tools or time, although this would typically indicate a broader breach at the site level. This means that trust must come from the system architecture, not only from the room’s level of visibility.
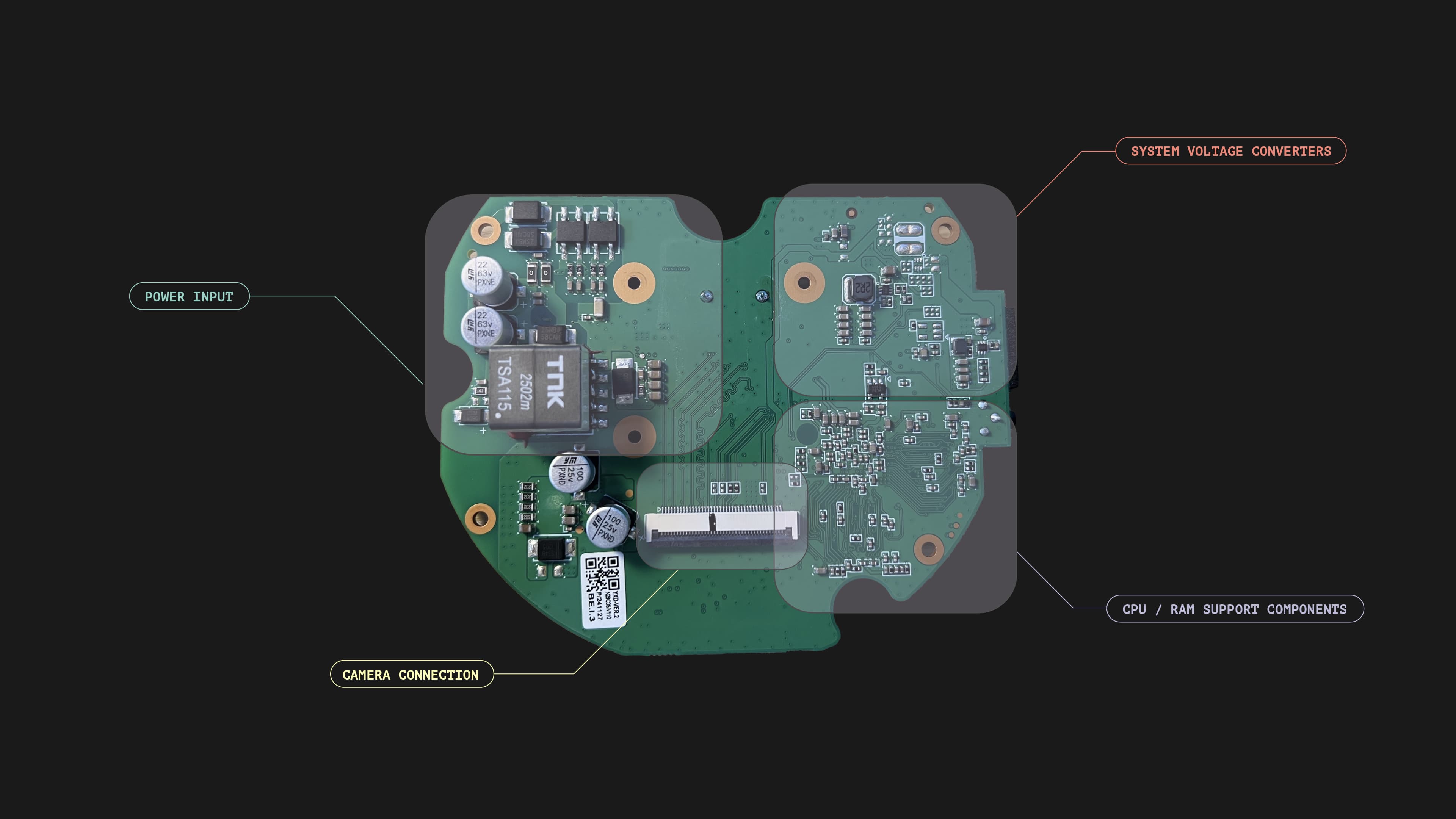
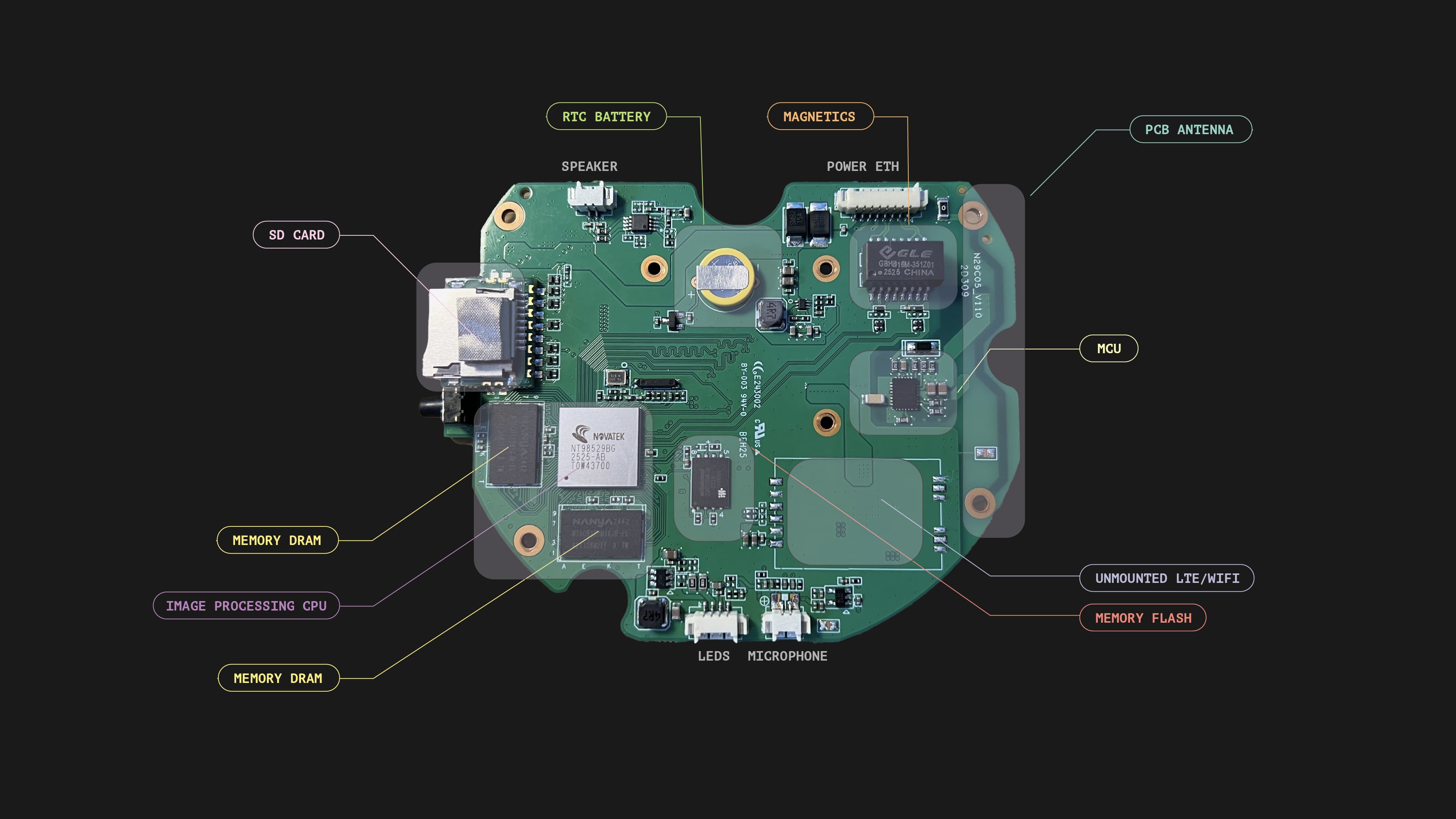
The supply chain adds another dimension. Every device is built from components that pass through multiple hands, and we rely on external partners for parts of the process and components. A realistic threat model must include the possibility of manipulation during these steps. We need predictable hardware, trustworthy partners, and consistent manufacturing practices.
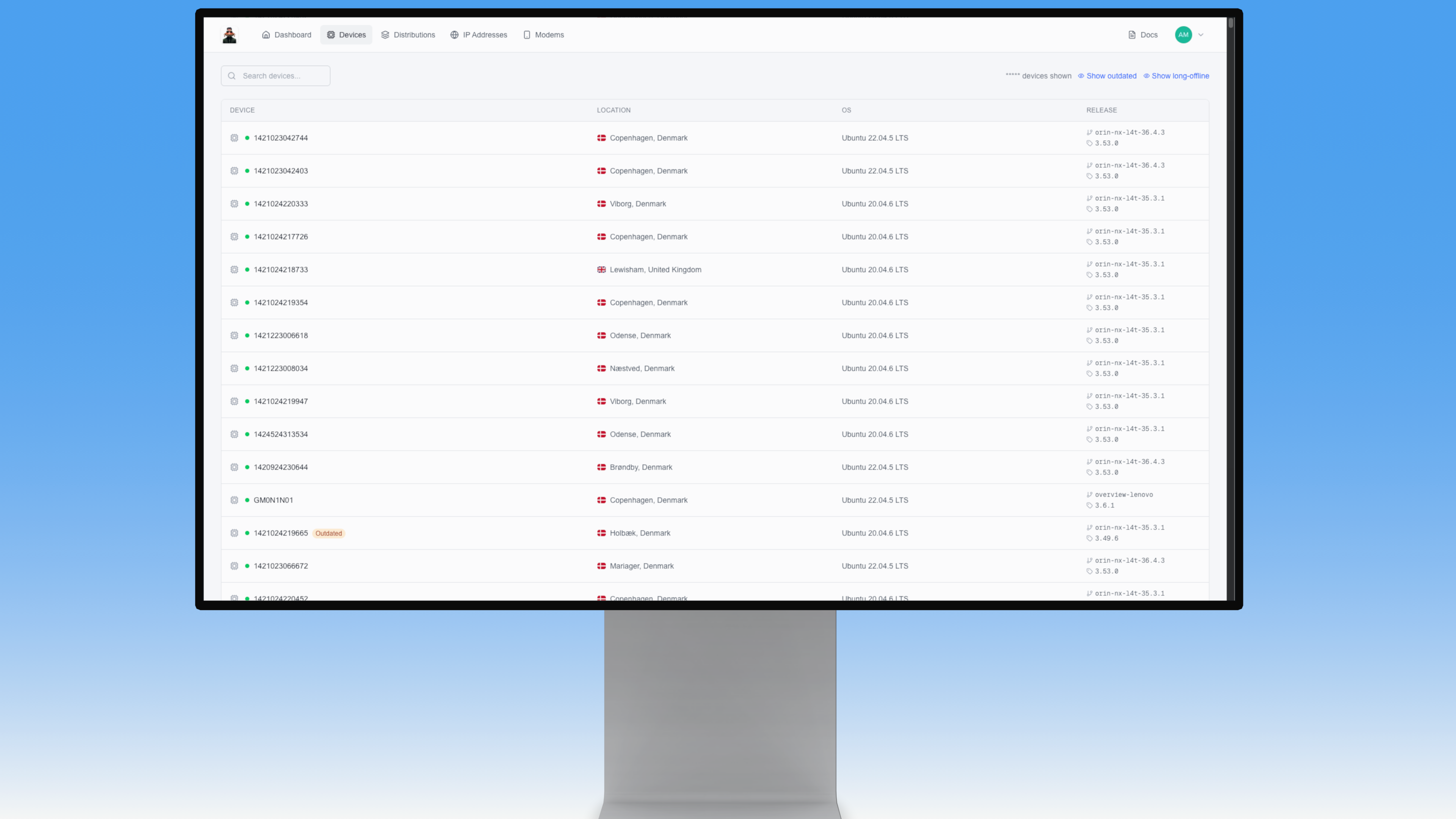
Because we operate a large fleet of IoT devices, we also need to consider fleet effects. A network is only as strong as its weakest links. We design with the assumption that a single compromised unit must not grant access to any other device, any sensitive data, or any part of the broader system.
Finally, because we operate in healthcare settings, privacy is part of the threat model from the start. Devices should not hold information that could identify people or expose clinical details. Even in a worst-case scenario involving physical access or full compromise, an attacker should not be able to learn anything meaningful about the person in the room.
This may seem like a lot, but taking security seriously also means being transparent about the risks and clear about how we address them.